Triplet Censors: Demystifying Great Firewall’s DNS Censorship Behavior
 GFW Triplet Censors
GFW Triplet Censors
Abstract
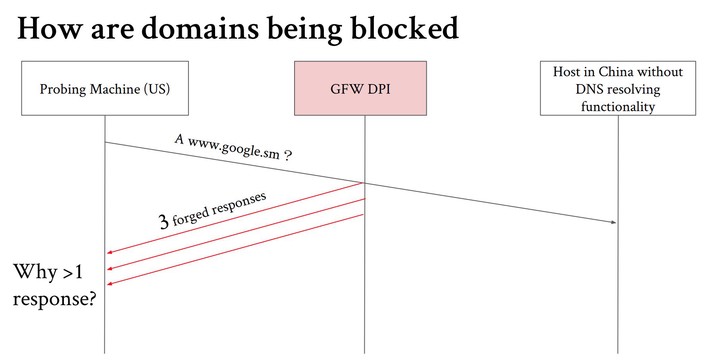
The Great Firewall of China (GFW) has long used DNS packet injection to censor Internet access. In this work, we analyze the DNS injection behavior of the GFW over a period of nine months using the Alexa top 1M domains as a test list. We first focus on understanding the publicly routable IPs used by the GFW and observe groups of IPs used to filter specific sets of domains. We also see a sharp decline in public IPs injected by the GFW in November 2019. We then fingerprint three different injectors that we observe in our measurements. Notably, one of these injectors mirrors the IP TTL value from probe packets in its injected packets which has implications for the use of TTL-limited probes for localizing censors. Finally, we confirm that our observations generally hold across IP prefixes registered in China.